Is an open source tool to help you build a valid SSL certificate chain from the root certificate to the end-user certificate. Also can help you fix the incomplete certificate chain and download all missing CA certificates.
How To Use
It's simple:
# Clone this repository
git clone https://github.com/trimstray/sslmerge
# Go into the repository
cd sslmerge
# Install
./setup.sh install
# Run the app
sslmerge -i /data/certs -o /data/certs/chain.crt
- symlink to
bin/sslmergeis placed in/usr/local/bin- man page is placed in
/usr/local/man/man8
Parameters
Provides the following options:
Usage:
sslmerge <option|long-option>
Examples:
sslmerge --in Root.crt --in Intermediate1.crt --in Server.crt --out bundle_chain_certs.crt
sslmerge --in /tmp/certs --out bundle_chain_certs.crt --with-root
sslmerge -i Server.crt -o bundle_chain_certs.crt
Options:
--help show this message
--debug displays information on the screen (debug mode)
-i, --in add certificates to merge (certificate file, multiple files or directory with ssl certificates)
-o, --out saves the result (chain) to file
--with-root add root certificate to the certificate chainHow it works
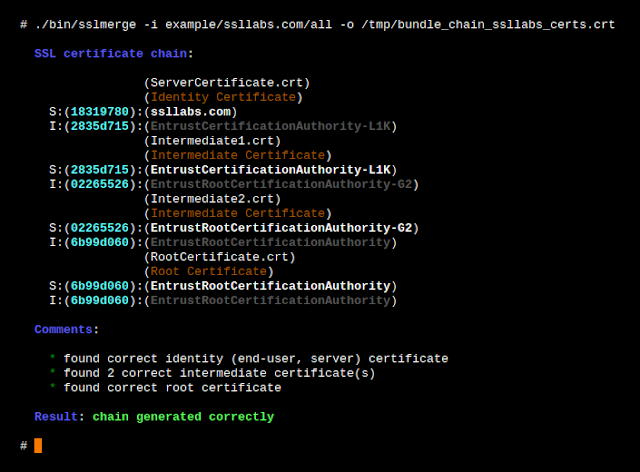
Let's start with ssllabs certificate chain. They are delivered together with the sslmerge and can be found in the
example/ssllabs.com directory which additionally contains the all directory (containing all the certificates needed to assemble the chain) and the server_certificate directory (containing only the server certificate).The correct chain for the ssllabs.com domain (the result of the openssl command):
Certificate chain
0 s:/C=US/ST=California/L=Redwood City/O=Qualys, Inc./CN=ssllabs.com
i:/C=US/O=Entrust, Inc./OU=See www.entrust.net/legal-terms/OU=(c) 2012 Entrust, Inc. - for authorized use only/CN=Entrust Certification Authority - L1K
1 s:/C=US/O=Entrust, Inc./OU=See www.entrust.net/legal-terms/OU=(c) 2012 Entrust, Inc. - for authorized use only/CN=Entrust Certification Authority - L1K
i:/C=US/O=Entrust, Inc./OU=See www.entrust.net/legal-terms/OU=(c) 2009 Entrust, Inc. - for authorized use only/CN=Entrust Root Certification Authority - G2
2 s:/C=US/O=Entrust, Inc./OU=See www.entrust.net/legal-terms/OU=(c) 2009 Entrust, Inc. - for authorized use only/CN=Entrust Root Certification Authority - G2
i:/C=US/O=Entrust, Inc./OU=www.entrust.net/CPS is incorporated by reference/OU=(c) 2006 Entrust, Inc./CN=Entrust Root Certification Authority- Identity Certificate (Server Certificate)
issued for ssllabs.com by Entrust Certification Authority - L1K
- Intermediate Certificate
issued for Entrust Certification Authority - L1K by Entrust Root Certification Authority - G2
- Intermediate Certificate
issued for Entrust Root Certification Authority - G2 by Entrust Root Certification Authority
- Root Certificate (Self-Signed Certificate)
issued for Entrust Root Certification Authority by Entrust Root Certification Authority
Scenario 1
In this scenario, we will chain all delivered certificates. Example of running the tool:
Scenario 2
In this scenario, we only use the server certificate and use it to retrieve the remaining required certificates. Then, as above, we will combine all the provided certificates. Example of running the tool:
Certificate chain
In order to create a valid chain, you must provide the tool with all the necessary certificates. It will be:
- Server Certificate
- Intermediate CAs and Root CAs
However, if you look inside the generated chain after generating with sslmerge, you will not find the root certificate there. Why?
Because self-signed root certificates need not/should not be included in web server configuration. They serve no purpose (clients will always ignore them) and they incur a slight performance (latency) penalty because they increase the size of the SSL handshake.
If you want to add a root certificate to the certificate chain, call the utility with the
--with-root parameter.Certification Paths
Sslmerge allows use of two certification paths:
Output comments
When generating the chain of certificates, sslmerge displays comments with information about certificates, including any errors.
Here is a list of all possibilities:
not found identity (end-user, server) certificate
The message is displayed in the absence of a server certificate that is the beginning of the chain. This is a unique case because in this situation the sslmerge ends its operation displaying only this information. The server certificate is the only certificate required to correctly create a chain. Without this certificate, the correct chain will not be created.
found correct identity (end-user, server) certificate
The reverse situation here - message displayed when a valid server certificate is found.
not found first intermediate certificate
This message appears when the first of the two intermediate certificates is not found. This information does not explicitly specify the absence of a second intermediate certificate and on the other hand it allows to determine whether the intermediate certificate to which the server certificate was signed exists. Additionally, it can be displayed if the second intermediate certificate has been delivered.
not found second intermediate certificate
Similar to the above, however, it concerns the second intermediate certificate. However, it is possible to create the chain correctly using the second certification path, e.g. using the first intermediate certificate and replacing the second with the main certificate.
one or more intermediate certificate not found
This message means that one or all of the required intermediate certificates are missing and displayed in the absence of the root certificate.
found 'n' correct intermediate certificate(s)
This message indicates the number of valid intermediate certificates.
not found correct root certificate
The lack of the root certificate is treated as a warning. Of course, when configuring certificates on the server side, it is not recommended to attach a root certificate, but if you create it with the sslmerge, it treats the chain as incomplete displaying information about the incorrect creation of the chain.
an empty CN field was found in one of the certificates
This message does not inform about the error and about the lack of the CN field what can happen with some certificates (look at
example/google.com). Common Name field identifies the host name associated with the certificate. There is no requirement in RFC3280 for an Issuer DN to have a CN. Most CAs do include a CN in the Issuer DN, but some don't, such as this Equifax CA.Requirements
Sslmerge uses external utilities to be installed before running:
Other
Contributing
See this.
Project architecture
See this.
More information
- Hacker Tool Kit
- Ethical Hacker Tools
- Hacker Tools Hardware
- Hack Tools Pc
- Pentest Tools Kali Linux
- Pentest Tools Port Scanner
- Hacker Tools 2019
- Hacker Tools List
- Hack Tools Github
- Easy Hack Tools
- Pentest Tools Android
- Pentest Tools Github
- Hacking Tools
- Hacker Tools Windows
- Hacker Tools Hardware
- New Hack Tools
- Hack Tools For Ubuntu
- New Hacker Tools
- Easy Hack Tools
- Hacker Tools List
- Hack Tools
- Hacker Tools 2020
- Pentest Tools Website
- What Is Hacking Tools
- Pentest Tools For Windows
- Hack Tools Mac
- Android Hack Tools Github
- Hackrf Tools
- Bluetooth Hacking Tools Kali
- Pentest Recon Tools
- Hack Tools
- Nsa Hack Tools Download
- Hacker Tools Windows
- Hacker Tools Free
- Pentest Tools Online
- Hack Tools Online
- Hacking Tools For Windows 7
- Computer Hacker
- Hacking Tools 2019
- Tools For Hacker
- Hack Tools For Pc
- Pentest Tools Tcp Port Scanner
- Hacking Tools
- New Hack Tools
- Hacker Techniques Tools And Incident Handling
- Pentest Tools Apk
- Hacker Tools Mac
- Hack Tools
- Computer Hacker
- Hacker Tools Mac
- Hacker Tools For Pc
- Pentest Tools Nmap
- Hacking Tools Mac
- Pentest Tools Port Scanner
- Hacking Apps
- Hacking Tools For Kali Linux
- Tools Used For Hacking
- Pentest Tools Open Source
- Pentest Tools List
- Hacking Tools For Kali Linux
- Best Hacking Tools 2020
- Hacking Tools For Games
- Hacker Tools For Mac
- Hack Tools Online
- New Hack Tools
- Pentest Tools Kali Linux
- Hacking Tools Free Download
- Hack Tools Pc
- Pentest Automation Tools
- Hacking Tools Online
- Hacking Tools 2019
- Hack Tools For Games
- Pentest Tools Review
- Hacking Tools For Windows Free Download
- Pentest Reporting Tools
- Hack Rom Tools
- Hacker Tools Online
- Hack Tool Apk
- Nsa Hack Tools Download
- Pentest Tools Port Scanner
- Hacker Tool Kit
- Hacking Tools Download
- Top Pentest Tools
- Hacks And Tools
- Hack Rom Tools
- Hacking Tools Windows 10
- Hacking Tools Hardware
- Pentest Automation Tools
- Hacking Tools Software
- Top Pentest Tools
- Hack Tools Download
- Best Pentesting Tools 2018
- Hacker Tools 2019
- Underground Hacker Sites
- New Hacker Tools
- Hack Tools Pc
- Hack Tools Download
- Pentest Tools Nmap
- Nsa Hacker Tools
- Hacking Tools For Beginners
- Hacks And Tools
- Hack Rom Tools
- Nsa Hack Tools Download
- Hacking Tools For Mac
- New Hack Tools
- Hacker Security Tools
- Pentest Tools
- Pentest Tools
- Pentest Automation Tools
- Hacker Tool Kit
- Hacking Tools For Kali Linux
- Hacking Tools For Beginners
- Wifi Hacker Tools For Windows
- Hackrf Tools
- Hack And Tools
- Pentest Tools Subdomain
- Tools For Hacker
- Hacker Tools Apk
- Hacker Tools Windows
- Hack Tools For Windows
- Hacker Tools Github
- Hack Tools 2019
- Hack Tools Github
- Hack Tool Apk No Root
- Hacker Techniques Tools And Incident Handling
- Hacker Tools Free
- Pentest Tools For Windows
- Termux Hacking Tools 2019
- Pentest Tools Subdomain
- Computer Hacker
- Hack Tools For Ubuntu
- How To Make Hacking Tools
- Hackers Toolbox
- Hack Tools Mac
- Tools For Hacker
- Pentest Tools Subdomain
- Tools Used For Hacking
- Hacker Tools Online
- New Hacker Tools
- Top Pentest Tools
- Hack Tools Online
- Pentest Box Tools Download
- Hack Tools Mac
- Hack Rom Tools
- Hack Website Online Tool
- Hacking Tools For Windows 7
- Pentest Tools Bluekeep
- Hak5 Tools
- Hacking Tools Hardware
- Top Pentest Tools
- Github Hacking Tools
- New Hack Tools
- What Are Hacking Tools



No hay comentarios:
Publicar un comentario